In the ever-evolving cybersecurity landscape, staying ahead of threats is not just a best practice—it’s a necessity. Organizations grapple with various vulnerabilities that can expose their critical assets to malicious actors. Enter Tenable, a name that resonates with security professionals worldwide. In this comprehensive Tenable review, we’ll delve into the heart of Tenable, exploring its features, usability, real-world impact, pricing, and cons.
Why Vulnerability Management Matters
Before we dive into the specifics, let’s take a moment to appreciate the gravity of vulnerability management. Imagine your organization as a fortress, surrounded by a digital moat. Within that moat lie vulnerabilities—tiny cracks in the castle walls—that adversaries seek to exploit. These vulnerabilities could be unpatched software, misconfigurations, or weak access controls. A single breach could compromise sensitive data, disrupt operations, and tarnish your reputation.
Vulnerability management is the process of identifying, assessing, and mitigating these vulnerabilities. It’s akin to fortifying your castle, reinforcing weak points, and ensuring that your defenses remain robust. And that’s where Tenable steps in.
Meet Tenable: A Guardian Against Threats
1. The Tenable Arsenal
Tenable’s suite of tools equips security teams with the means to battle vulnerabilities head-on. Let’s unpack some of its essential components:
a. Vulnerability Scanning
Tenable’s vulnerability scanner prowls through your network, applications, and systems like a diligent sentry. It uncovers hidden vulnerabilities, shining a spotlight on weak spots. Whether it’s a forgotten server in the corner or a misconfigured firewall, Tenable’s scanner leaves no stone unturned.
b. Risk Assessment
Not all vulnerabilities are created equal. Some pose a minor inconvenience, while others threaten the very core of your infrastructure. Tenable’s risk assessment engine assigns scores based on severity, exploitability, and potential impact. This intelligence allows you to prioritize remediation efforts effectively.
c. Continuous Monitoring
Cyber threats don’t adhere to office hours. They lurk in the shadows, waiting for an opportune moment. Tenable’s real-time monitoring ensures that you’re never caught off guard. It alerts you when new vulnerabilities emerge, enabling swift action.
2. The User Experience
a. Navigating the Tenable Interface
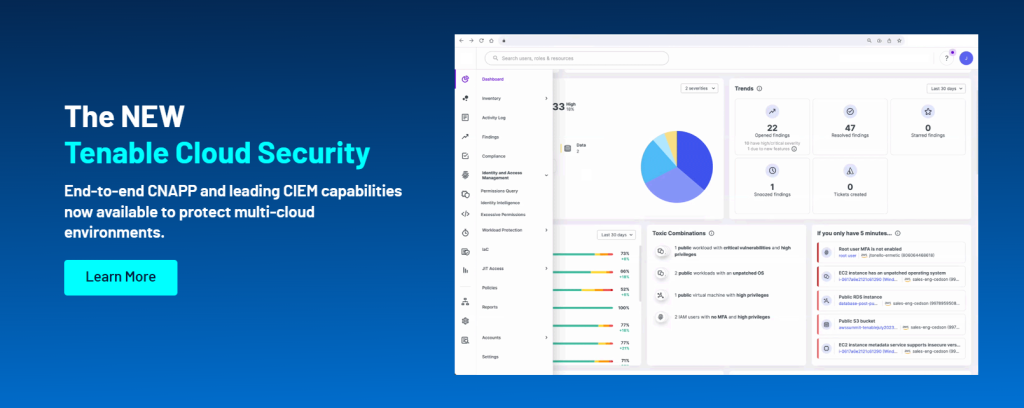
Imagine stepping into a cockpit—the controls are intuitive, the dials responsive. Tenable’s interface mirrors this simplicity. Whether you’re a seasoned security analyst or a curious IT manager, you’ll find your bearings swiftly. The dashboard provides a bird’s-eye view of vulnerabilities, risk trends, and compliance status. Widgets allow customization, so you focus on what matters most.
b. Asset Management Made Easy
Tenable’s asset discovery capabilities resemble a diligent librarian cataloging books. It identifies devices, categorizes them, and maintains an inventory. Tagging and grouping features help organize assets logically. Need to find all servers running outdated software? Tenable’s got your back.
3. Real-World Impact
Let’s step out of theory and into the field. Organizations across industries rely on Tenable to safeguard their digital realms:
- Scenario 1: A financial institution uses Tenable to scan its web applications regularly. The tool flags a critical vulnerability in the online banking portal—a potential gateway for cybercriminals. The team patches it swiftly, averting disaster.
- Scenario 2: An e-commerce giant leverages Tenable to assess vulnerabilities in its sprawling cloud infrastructure. By addressing high-risk issues, they ensure smooth transactions and customer trust.
Exploring Tenable’s Features: A Comprehensive Analysis
1. The User Interface and Navigation
a. Dashboard Overview
Imagine stepping into a control room—the hum of servers, the glow of monitors. Tenable’s dashboard is your command center, providing a panoramic view of your digital landscape. Let’s break it down:
- Widgets Galore: The dashboard is a mosaic of widgets, each revealing critical insights. From vulnerability trends to compliance status, these widgets keep you informed. Customize them to suit your preferences—like rearranging furniture in a familiar room.
- Risk Heatmap: Picture a weather map with varying shades—Tenable’s risk heatmap operates similarly. It visualizes vulnerabilities across your assets, highlighting hotspots. Red patches? High-risk areas. Green? You’re in the clear.
- Executive Summary: At the top, an executive summary awaits. It condenses complex data into digestible nuggets. Think of it as the “CliffsNotes” version for decision-makers.
b. Asset Management Made Easy
Managing assets can feel like herding digital cats. Tenable simplifies this task:
- Asset Discovery: Tenable’s scouts roam your network, identifying devices like diligent librarians cataloging books. Servers, routers, printers—they all get tagged and categorized. No more “Where’s that server hiding?”
- Tagging and Grouping: Imagine organizing your wardrobe by color or season. Tenable lets you tag and group assets logically. Need all Windows servers? Filter by tags. Want to see cloud instances? Group them. It’s like tidying up a cluttered room.
2. Vulnerability Scanning: The Sentinel’s Quest
a. Scheduled Scans
Tenable’s vulnerability scanner is like a tireless sentinel patrolling your digital borders. Set it loose on a schedule—daily, weekly, or whenever suits your castle. It probes every nook and cranny, flagging vulnerabilities. Forgotten web apps? Misconfigured routers? It spots them all.
b. Credentials Matter
Picture this: The sentinel approaches a guarded gate. Without proper credentials, it’s denied entry. Tenable understands this. For thorough scans, provide credentials—like handing the sentinel a VIP pass. Authenticated scans reveal hidden vulnerabilities, ensuring a robust defense.
c. Plugin Library: Spells and Incantations
Tenable’s plugin library resembles a wizard’s grimoire. Each plugin is a spell—an incantation to uncover vulnerabilities. Whether it’s a known software flaw or a misconfigured setting, these plugins work their magic. The library grows, adapting to emerging threats.
3. Reporting and Analytics: The Oracle’s Insights
a. Custom Reports
Tenable’s reporting engine weaves narratives. Imagine crafting bespoke reports for different audiences: the CEO, the IT team, and the auditors. Choose your metrics, weave your tale, and present it elegantly. It’s like writing a captivating chapter in your security saga.
Tenable Detailed Pricing Plan :
Let’s explore the pricing plan in a very detailed way to help you choose the best price according to your tailored needs.
1. Tenable Nessus Professional
Tenable Nessus Professional is the industry’s most widely deployed vulnerability scanner. It combines broad coverage, rapid updates, and an easy-to-use interface. Here are the pricing details:
- 1 Year License: $3,990
- 2 Years License: $7,780.50
- 3 Years License: $11,371.50
Support and Training Add-Ons:
- Advanced Support: For $400, you get 24×365 access to phone, email, community, and chat support.
2. Tenable Nessus Expert
Tenable Nessus Expert is designed for the modern attack surface. It fortifies web applications, provides visibility into internet-connected assets, and secures cloud infrastructure. In addition to all the features of Nessus Professional, it offers the following:
- External Attack Surface Scanning
- Ability to Add Domains
- Web Application Scanning
- Scan Cloud Infrastructure
- 500 Prebuilt Scanning Policies
Pricing for Tenable Nessus Expert:
- 1 Year License: $5,990
- 2 Years License: $11,680.50
- 3 Years License: $17,071.50
Support and Training Add-Ons:
- Advanced Support: Available for $400
3. Tenable Vulnerability Management
Tenable Vulnerability Management provides accurate information about all your assets and vulnerabilities in dynamic environments. Here’s the pricing for up to 250 assets:
- 100 Assets Subscription:
- 1 Year: $3,500
- 2 Years: $6,825
- 3 Years: $9,975
4. Tenable Web App Scanning
Gain visibility into the security of web applications with safe vulnerability scanning. The pricing for scanning 5 Fully Qualified Domain Names (FQDNs) is $3,578.
Visit Tenable for more detailed pricing
Remember that these prices may vary based on specific requirements and additional features.
Cons Of Tenable:
Certainly! Let’s explore some of the cons associated with Tenable, the vulnerability management solution:
- Learning Curve:
- Tenable’s feature-rich environment can be overwhelming for new users. The learning curve might be steep, especially for those unfamiliar with vulnerability management tools.
- Complexity of Reporting:
- While Tenable offers extensive reporting capabilities, creating customized reports can sometimes require manual effort. Exporting and analyzing data for dashboards may not be as straightforward as desired.
- Cloud Scanning Limitations:
- Tenable’s current version lacks native support for cloud scanning, especially for platforms like AWS. Organizations heavily invested in cloud infrastructure may find this limitation restrictive.
- External Tools Integration:
- Some users find that certain built-in components within Tenable could benefit from better integration with external tools. Streamlining these components would enhance the overall user experience.
Remember that these cons should be considered alongside Tenable’s strengths and the specific needs of your organization.
